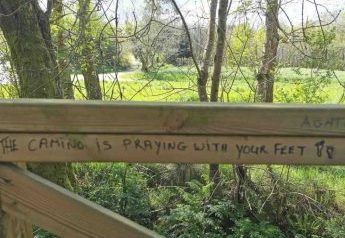
Solvitur Ambulando; Sanatus Ambulando
“When you’re on the Camino Santiago, which is more than 1000 years old, you’re immersed in the embrace of the past, the present and the future. You’re also primed to walk in all three temporalities.” ~ timothy khoo “Solvitur Ambulando” is a Latin phrase that literally translates as “it is solved by walking.” It is attributed … Read More
A Letter to My Younger Self ~ Adele Tan-Nair
One beautiful expression of the internal journey is the writing of a letter to our younger self. Lessons we’ve learnt along the way that would have helped us navigate life in our younger perhaps bewildered days. This is a letter from one of the sojourners who just completed the Camino Santiago with desert odyssey.
Walking at the Speed of Friendship
“What is humanity, really, but a family of families?” ~ Vivek Murthy (US Surgeon General) In a recent article in The Atlantic on friendship, the author notes, “In the hierarchy of relationships, friendships are at the bottom. Romantic partners, parents, children—all these come first. Friendships are unique relationships because unlike family relationships, we choose to enter into them. And unlike … Read More
A Collection of Poems and Prose ~ reflections from a desert odyssey sojourner
The thirty-ninth desert odyssey (April 1-8, 2023), was convened over Holy Week in Jeju, Korea. Each day bore witness to unfamiliar perspectives on familiar topics. This blog post is the unsolicited reflections of a sojourner.
Walking at the Speed of a Child
“Unless you change and become like a little child….” ~ Jesus On February 28th, 2023, what was old became new. A friendship forged 34 years ago, nurtured in shared vision, disrupted by time, distance, and drift, forged in mutual adversity, now rekindled in reconnection. My brother, Dinesh, who saw beyond his legal profession, left that security … Read More
Walking at the Speed of Life
“Not all who wonder, or wander are lost.” ~ JRR Tolkien For over a thousand years, many have walked the Camino Santiago (including one I draw immense inspiration from – Francis of Assisi – who walked the Camino from Italy to Santiago, Spain in 1214). Walking the Camino as a pilgrim (or peregrino as those … Read More
“The gods envy us…”
“The gods envy us. They envy us because we’re mortal, because any moment may be our last. Everything is more beautiful because we’re doomed. You will never be lovelier than you are now. We will never be here again.” ~ Homer, The Iliad Across the street from my son’s apartment in Nova Scotia, Canada, is … Read More
On Being Real ~ The Tale of the Satin Rabbit (Based on the book ‘The Velveteen Rabbit’ by Margery Williams)
“THERE was once a velveteen rabbit, and in the beginning he was really splendid. He was fat and bunchy, as a rabbit should be; his coat was spotted brown and white, he had real thread whiskers, and his ears were lined with pink sateen.”* Pre 2014, I was the velveteen rabbit, or in my case, … Read More
Diamond Dust ~ reflections from a desert odyssey sojourner
The thirty-fifth desert odyssey (January 16-22, 2022), was a non-residential edition held at the desert odyssey space here in Singapore. It included one sojourner who ‘Zoomed’ in from Sydney, Australia. These two poems were penned by her as she experienced the liberating journey from excruciating to exquisite pain!
How To Want Less
Abd al-Rahman III, the emir and caliph of Córdoba in 10th-century Spain, summed up a life of worldly success at about age 70: “I have now reigned above 50 years in victory or peace; beloved by my subjects, dreaded by my enemies and respected by my allies. Riches and honors, power and pleasure, have waited … Read More
Holy Week desert odyssey ~ 10-16 April 2022
Holy Week has always been a special time to convene desert odyssey. Here, we explore moving in rhythm with time as it’s meant to be lived – Kairos rather than Chronos. To find out more, email info@desertodyssey.com
Reflection & Decision
The time has come for honest reflection on the year(s) past and decisions for what’s ahead. With an eye to the etymology of “decide” — which stems from the Latin decidere, “to cut off,” a root it shares with “homicide” and “suicide” — I am led to consider the necessity of excision. Oliver Burkeman poignantly … Read More
Actio Sequitur Esse – Action Follows from Essence
(Article by timothy khoo, published in August 2021 in the Law Gazette, the official publication of the Law Society of Singapore) In the Disney Pixar movie, “Soul”, the main characters, Joe and Soul 22 are engaged in dialogue in the fantastical place called The Great Before. Soul 22 turns to Joe and says, “You can’t … Read More
Falling Into Grace
“My fall into grace, quite paradoxically, is probably the reason I will finish stronger than if I hadn’t fallen into grace,” Timothy Khoo reflected when asked about the moral failure he experienced. “I fell into grace. And I remained there. And tasted the incredible love of God.” What would your authentic self be if stripped … Read More
this being human….
So begins a poem by rumi. This human being needs to learn more about being human. Yet it is also a season of unlearning. If knowledge is about learning, then wisdom is about unlearning. There is a lot I have to unlearn. In this next season (without forethought of how long it will last), this … Read More
The Kintsugi Journey
This supplemental programme to desert odyssey leverages the experiential aspect of learning. For more information on the programme, you can contact us via the Whatsapp button on this page or email the address given in the flyer.
Dopamine Nation: Finding Balance in the Age of Indulgence
A fascinating article that examines the pain~pleasure balance we explore in some depth at desert odyssey. Read on for practical advice on recalibrating and finding balance. “The smartphone is the equivalent of the hypodermic needle, delivering digital dopamine 24/7 for a wired generation.” Link
December 26th, 2020
One of the desert odyssey sojourners posed a question as to how we might see the juxtaposition of this pandemic and the meaning of Christmas. We’ve long forgotten that the first Christmas was more akin to what we’re experiencing now than what we’ve taken for granted in recent years. Foreign occupation then (Romans), foreign occupation … Read More
Living Your Eulogy Not Your Resume
The thirtieth desert odyssey (August 1-9, 2021), was a non-residential edition held at the desert odyssey space here in Singapore. This reflection is from one of the sojourners, and captures powerfully the experience of deep and liberating insights!
Conversation Six ~ The Three Equations
Conversation Six (in the Desert Odyssey virtual relational platform series) ~ The Three Equations How do we maintain safe distancing but retain communal connectedness and social solidarity? How do we emerge from this crisis not just relieved and returning to our old patterns of behaviour and consumption with a vengeance, but to emerge a better … Read More
Conversation Five ~ The Moral Meaning of the Plague
Conversation Five (in the Desert Odyssey virtual relational platform series) ~ The Moral Meaning of the Plague Human beings have a need to make sense of the world around them. But is there always a purpose for events that happen that may at times appear random? At Desert Odyssey, we delve into the essential difference … Read More
Conversation Four ~ Maturity & COVID-19
Conversation Four (in the Desert Odyssey virtual relational platform series) ~ Maturity & COVID-19 “Instead of resisting to changes, surrender. Let life be with you, not against you. If you think ‘My life will be upside down’ don’t worry. How do you know down is not better than upside?” ~ Shams of Tabriz “As people’s … Read More
Conversation Three ~ Collateral Beauty
Conversation Three (in the Desert Odyssey virtual relational platform series) ~ Collateral Beauty In a world that values and even worships strident individualism, how do we bridge the divide and the space between that individualism and our human connectedness? It has become clear hasn’t it, that even the virus connects us, yet we deny the … Read More
Conversation Two ~ Living in the Everlasting Present
Conversation Two (in the Desert Odyssey virtual relational platform series) ~ Living in the Everlasting Present “There is no future!!” someone opined with a sense of deep resignation as the pandemic perpetuates. What this person really meant was that it’s hard if not virtually impossible to plan for the future under the current conditions (even … Read More
Conversation One ~ Pandemic
Conversation One (in the Desert Odyssey virtual relational platform series) ~ Pandemic Pandemicby Lynn Ungar March 11, 2020 What if you thought of it as the Jews consider the Sabbath—the most sacred of times?Cease from travel.Cease from buying and selling.Give up, just for now,on trying to make the worlddifferent than it is.Sing. Pray. Touch only … Read More
Falling Into Grace
(Article by timothy khoo, published in the Methodist Message in August 2019) “Do you believe that God loves you beyond worthiness or unworthiness, beyond fidelity or infedility? Do you believe that he loves you in the morning sun and the evening rain? Do you believe that he loves you when your intellect denies it, your … Read More
Falling into grace: What moral failure taught a reverend about God
“Nobody wants to be defined by the worst thing they’ve ever done. But on this side of heaven, that’s often the case – the worst thing you’ve ever done defines you,” Reverend Timothy Khoo quietly told a small crowd of about 50. They had gathered to hear him share at an Eagles Leadership Conference 2019 … Read More
Reflections of a Wo(a)ndering Sojourner
Sitting at Ya Kun (a local coffee place), because I couldn’t get into a Christmas Musical at a local church. Reminded in a small way of that first Christmas where there was no room in the inn. A week ago, for the first time since I was 21 (33 years ago), I am without … Read More